Your Firefox Just Became a Welcome Mat! Update It Now!
Are you still running outdated software while whispering hopeful prayers at your screen? Mozilla just released Firefox ESR 140.9.1 on April 7, 2026. This is not a routine housekeeping update. This is the digital equivalent of replacing your front door lock after discovering it opens from both sides.
Let’s skip the jargon theater and talk about what actually happened.
Security Vulnerabilities: CVE-2026-5732
When Numbers Lose Their Minds
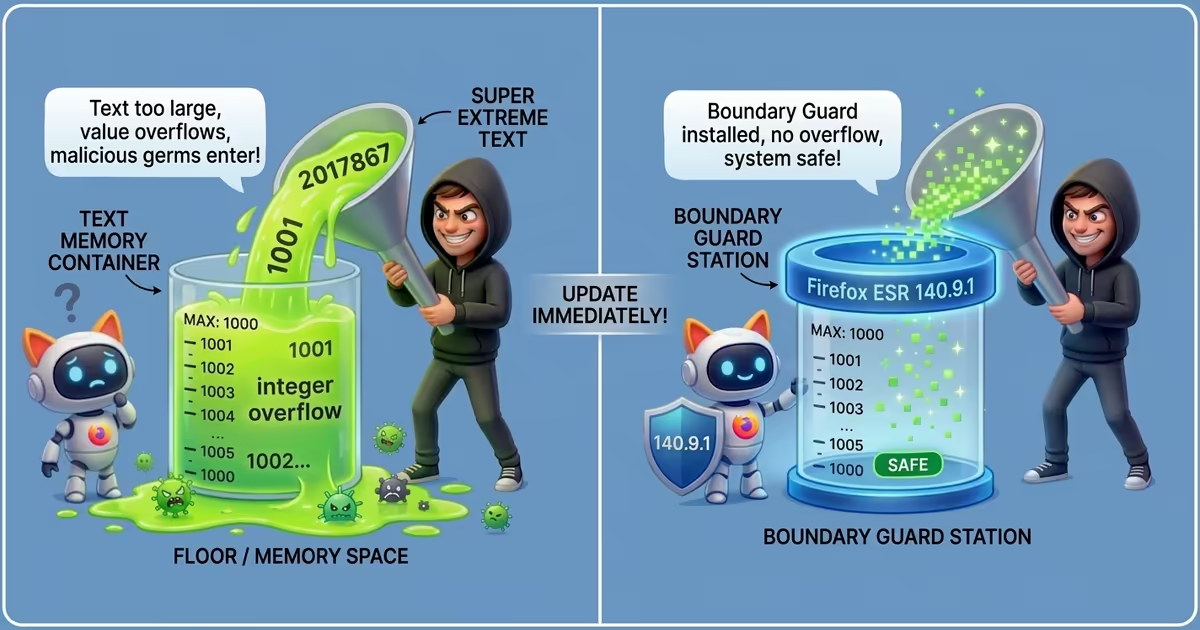
Every digital container holds a maximum value. Push past that limit and something breaks — not gracefully, not quietly. The number panics, resets to zero, or jumps somewhere wild. This is called an integer overflow, and Firefox ESR 140.9.0 had one hiding inside the component that draws text on your screen.
Maliciously crafted text. That’s all it takes.
No suspicious download. No phishing link. No fake Nigerian prince requiring your bank details. You visit a webpage. The page contains specially poisoned text formatting. Firefox chokes on the oversized number, its internal defenses shatter, and a hacker slides through the wreckage like someone walking through a wall that was never properly built.
That’s rated high-impact for good reason. Your machine doesn’t need to cooperate — it just needs to be on.
Security Vulnerabilities Fixes: CVE-2026-5731
The Locker Room Where Anyone Can Open Anyone’s Locker
Think of computer memory as a gym with hundreds of rental lockers. Every application gets a specific locker and a matching key. This vulnerability is the faulty lock that opens for the wrong key — or no key at all.
This bug didn’t politely limit itself to Firefox. It infected Firefox 149.0.1, Thunderbird 149.0.1, and the older ESR 115.34.0. A wide net of vulnerable targets sitting in offices, hospitals, schools, and living rooms across the planet.
Unpatched, this flaw lets criminals force your browser into running secret code. Spy on activities. Harvest stored passwords. Borrow your session silently while you believe you’re safely browsing a recipe website.
The gym manager — in this analogy — is the patch. Install it and the broken locks get replaced before the next thief notices the opening.
Security Vulnerabilities Fixes: CVE-2026-5734
The Restaurant That Never Clears Its Tables
Modern browsers juggle enormous amounts of data. Open a tab, stream video, click a link — memory is borrowed and returned thousands of times per minute. The system works beautifully when everyone cleans up after themselves.
CVE-2026-5734 is the negligent waiter who forgets to clear the table. Memory gets marked as active when it’s actually empty. The system doesn’t notice. The hacker does.
Picture a busy restaurant. A customer finishes, pays, and leaves. The waiter ignores the dirty table. The hostess seats the next guest without checking. A stranger slips a poisoned menu onto the uncleaned surface. The new customer picks it up, reads it, and the damage is done.
This flaw spread across both standard Firefox and ESR releases, plus Thunderbird. The fix fires the negligent waiter and installs a strict manager who wipes every memory slot clean before the next user arrives.
The Part Where IT Departments Need to Stop Playing Theater
Corporate IT has a curious talent for delaying critical patches to avoid “minor disruptions” — while leaving digital doors wide open for criminals with patience and skill. The logic is roughly equivalent to refusing to change a broken door lock because the locksmith appointment might interrupt lunch.
CVE-2026-5732, CVE-2026-5731, and CVE-2026-5734 are not theoretical threats. They are documented, weaponizable, and actively sought by people who do not care about your lunch schedule.
Mozilla fixed them. The update exists. The only remaining question is whether your organization treats security as urgent reality or as bureaucratic paperwork requiring three levels of approval and a committee meeting.
Spoiler: the hacker is not waiting for the committee.
One Action. Today!
Check your Firefox version right now. If it reads anything below 140.9.1, you are operating with known, exploitable vulnerabilities.
Update. Restart. Done.
No megaphone needed. No press release required. No ribbon-cutting ceremony for a new Ministry of Browser Security. Just one update that takes under three minutes and removes three documented pathways for criminals to hijack your machine.
Your digital survival doesn’t need a symposium. It needs ten seconds and a click.
Think Deeply. Live Lightly — and patch promptly.
Thanks for reading (or maybe you just blinked and scrolled — I’ll never know). If you think the post rambled or needs a reality check, or the quiz was unfair, feel free to leave a note. I’m a teacher who loves learning from the brave souls who comment.